I’ve written about immigration policy before, and this is not that kind of post.
Instead, I am addressing a conventional fiction that “there is no wall” on the border of Mexico and the US. I’ve found that this is a surprisingly widespread belief.
The border
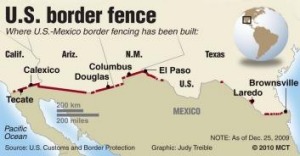
The total length of the border is just under 2,000 miles. Roughly half of that distance is the Rio Grande (which gave rise to the derogatory term for Mexican immigrants, wetback, as many illegals used to swim the river to get to the US).
Securing the border
In 1994, a National Border Patrol Strategic Plan started the process of improving security on the border to stem the flow of illegal immigration. The post-9/11 war on terror gave this attempt a big boost, with the Bush administration pushing hard to build a fence and ultimately passing a series of laws.
In other words, we have had legislation in place for many years to build the wall. And it’s largely funded.
Quite a bit of the wall has been built
So far, the US has built roughly 600 miles of fence. Taking out the river, we’re more than halfway there.
(The remaining land is handled by the Border Patrol and various infrared and technical contraptions.)
The Rio Grande
Now, here’s where it gets complicated:  We have this big river, the Rio Grande.
We have this big river, the Rio Grande.
Putting a fence in a river causes all kinds of environmental problems, which even if you’re a conservative, are cause for some concern (I live in Florida, and have seen the damage that the Tamiani Trail did to the Everglades, and while a porous fence isn’t nearly as bad as a dam, there are some real issues at stake here.)
No worries! In 2006, the Real ID Act was passed, which, in part, gave the Secretary of Homeland Security (then Michael Chertoff) the ability to waive environmental regulations in this context. He really wanted a wall, so he did just that.
Yet, we still don’t have a fence completed.
A major problem is the fact that there are three Native American reservations that sit on the border in Arizona. This leaves a gap in the “wall” which is occupied by sovereign Indian nations.
Most notable is the Tohono O’odham reservation, which is huge — about the size of Connecticut — and includes the vast Sonora Desert. Citing its sovereignty, it once successfully barred the Border Patrol from entering the reservation. They’ve since changed their tune, since now, this opening in the border has driven drug smugglers into the area (as well as illegals, who are dying in the thousands trying to cross the Sonoran Desert).
This is a major issue: we have to figure out a way to build a wall through a sovereign Indian nation. It’s not insignificant. Imagine a wall going through your own neighborhood — the Native Americans are not crazy about this idea. And we can’t move the border south, nor north. It has to be a wall right through these Indian nations.
In other words, it’s a bit more complicated than a simple stump speech.
My Dystopian Vision
 I talked to a Trump supporter recently in San Francisco. I asked him how he thought Trump would fix the economy.
I talked to a Trump supporter recently in San Francisco. I asked him how he thought Trump would fix the economy.
“He’s going to get rid of all those fucking illegal immigrants,” he said, enthusiastically*.
So here’s my dystopian vision:
Trump enters office. Since “The Wall” is already approved and funded (by us, not Mexico, who will tell us to fuck off), it finally gets built.
Yay for Trump.
But then there’s the nagging problem of all of those “fucking illegals”. Trump wants forced deportation.
The last time that happened, the program, Operation Wetback, was stopped after Mexicans started dying in a trial of tears (we’re so good at this trial of tears thing, aren’t we?).
But what if, as some speculate, the military or others won’t follow his orders?
I see those, like my San Francisco Trump supporter, who will become effectively “brown shirts” for Mr. Trump.
I’m not making this up. Look at the protests. Watch Cartel Land, with citizen paramilitary outfits taking shots at Mexicans. The stuff going on right now is crazy.
Perhaps they will be called “Trumpeters” or some such name. I expect they will bang on the doors, wrench the illegals out of their homes, and probably engage in a bit of good old-fashioned pillaging.
Outlandish? Not really. We’ve had plenty of paramilitary groups in our nation’s history.
It’s only one of the disasters I foresee with a Trump presidency.
————–
* A silly statement. Getting rid of 11 million illegals will do nothing positive for our economy. It might very well crater it. The real problems — the massive national debt, the Federal Reserve hell-bent on printing money into ridiculous asset bubbles, massive spending on the military instead of national infrastructure, well… those are some of the real problems. Further simplistic arguments by Trump about taking on waste and fraud in the government? A drop in the bucket.
I’m not in favor of illegal immigration at all, but getting rid of the people who pick our lettuce, wash our dishes and clean our cars isn’t going to do a thing to help the economy. Illegals are easy scapegoats, they always have been, but they are not the correct reason WHY things aren’t going well in our country.



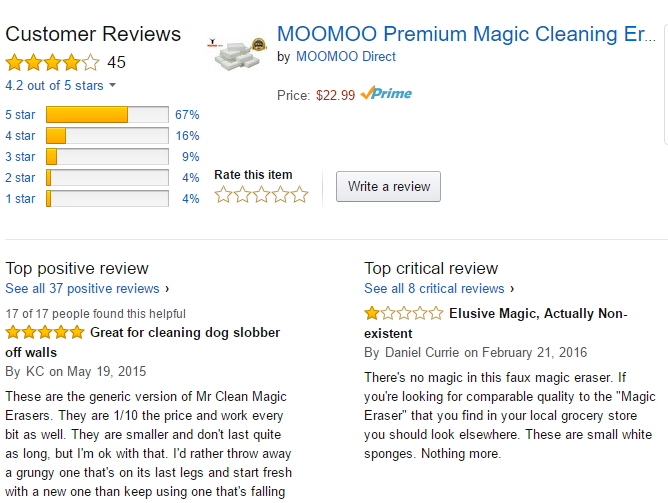


 Interesting overview
Interesting overview 



![The Author Rank Building Machine [INFOGRAPHIC] The Author Rank Building Machine #verticalmeasures #Infographic #Authorrank](http://www.verticalmeasures.com/wp-content/uploads/2013/11/The-Author-Rank-Building-Machine.gif)